Electronic Communication Network (ECN) - How To Discuss
Electronic Communication Network (ECN),
Definition of Electronic Communication Network (ECN):
Any one of several computer-based order matching systems that provides investors with direct access to the market, bypassing the middleman (broker) for order placement. With ECN access, investors can see quotes for the best bid and best ask and enter orders directly into the system. As a result, the ECN can speed up the order entry and ■■■■■■■■■ process as well as making it possible for investors to participate in extended trading hours. Each brokerage firm is free to decide which ECN it chooses to include in its order flow system and how much access to the ECN it will provide to its customers.
Meaning of Electronic Communication Network (ECN) & Electronic Communication Network (ECN) Definition
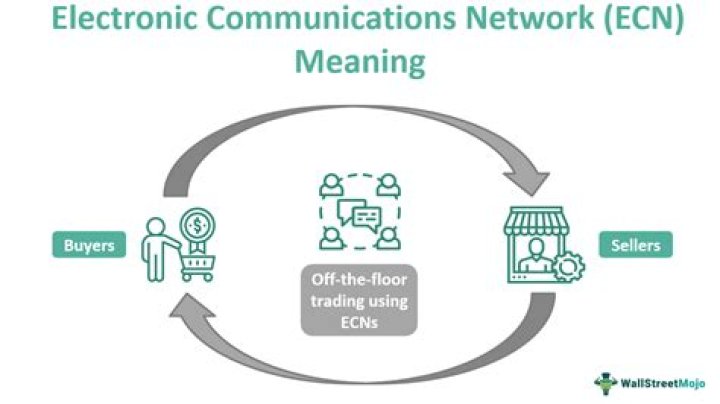
Electronic Communication Network (ECN) is a computerized forum or network that allows financial items to be traded outside traditional stock exchanges. Electronic Communication Networks are typically passive computer-driven networks that match limit orders internally and levy a very tiny per share transaction cost.
What is Electronic Communication Network
An Electronic Communication Network (ECN) is a computerized forum or network that allows financial items to be traded outside traditional stock exchanges.
An Electronic Communication Network is a broad term for an electronic meeting system that disseminates orders made by market makers to third parties and allows them to be administered in whole or part. Stocks and currencies are the most common goods traded on Electronic Communication Networks.
Instinet, the first Electronic Communication Network, was established in 1969. Electronic Communication Network s boost trading company competitiveness by cutting transaction costs, providing customers with full access to their order books, and providing order matching outside of regular exchange hours.
History of ECN
The sec defined Electronic Communication Network as “any electronic system that broadly disseminates to third parties orders placed therein by an exchange market maker or otc market maker, and authorizes such orders to be beheaded in whole or in part.”
The fostered the expansion of Electronic Communication Networks by changing regulatory regulations, and in 1975 the sec approved the securities acts amendments of 1975, supporting the “linking of all markets for qualifying securities through communication and data processing facilities.”
Through their relationship with NASDAQ, Electronic Communication Network s has complicated stock exchanges. The NASDAQ over-the-counter quote system was a significant milestone in the history of Electronic Communication Networks.
Function of ECN
Electronic Communication Networks are stock exchanges that allow for off-the-floor trading. To trade with an Electronic Communication Network, you must be a subscriber or have a trading account with a broker that offers direct access trading.
Unmatched orders will be posted on the system for other subscribers to view by the Electronic Communication Network. Buyers and sellers can trade anonymously via Electronic Communication Network, with trade records naming the Electronic Communication Network as the party.
Electronic negotiation, a sort of communication between agents that facilitates cooperative and competitive sharing of information to find a reasonable price, is often used to support Electronic Communication Network s.
Communication Process for virtual Organization
| Researchon Electronic Communication | Implications for Virtual Organizations |
|---|---|
| 1. Communication volume and efficiency - In electronic communication settings, volume tends to increase and efficiency tends to decrease 2. Message understanding - Message bias decreases but comprehension are more difficult (relative to face- to face). Impression formation takes longer Social context is critical. | Highly dynamic recesses - Managing communication load and meaning will be difficult as business processes change repeatedly. Message understanding may go down (at least initially) when processes change We can expect simultaneous pressures to routinize and personalize communication |
| Virtual tasks Some tasks are performed less effectively when done electronically; for example, consensus formation | Contractual relationships Some tasks may not lend themselves to performance across boundaries; design of contracts may have to vary by task, with some more formal (legal) and others more informal (psychological). |
| Lateral communication - broader, more diverse participation is likely; less domination and hierarchy in electronic communication (though these are not entirely eliminated) Norms of technology use- styles of technology use emerge in individuals, groups, and organizations | Edgeless, permeable boundaries More boundary spanning likely, broader, more functionally and culturally diverse parties will communicate Conflicts are likely if communication norms that are formed in different locations are not compatible. |
| Evolutionary effects- Impressions of others, impression management, and the degree and type of relational communication all change over time. Interpersonal relationships deepen Norm $ develop. | Reconfigurable structures - Reliable communication norms may be difficult to develop if redesign occurs too rapidly, use of communication histories may help to shorten evolutionary time periods the following redesign. |
Summary
ECN trading is especially useful when investors from different geographic regions want to conduct a secure transaction without the use of a third party.
Technologies of Electronic Communication Network
The field of autonomous agents has devoted particular attention to simulating automated discussions. If discussions often occur, maybe on a minute-by-minute basis to arrange network capacity, or if negotiation themes are well defined, it may be advantageous to automate this coordination.
In complex systems made of autonomous agents, automated negotiation is a critical kind of interaction. Negotiation is the practice of making offers and counteroffers to reach an acceptable agreement.
![:arrow_right: :arrow_right:]() In The Stock Exchange
In The Stock Exchange
Electronic Communication Networks are a type of sec-approved alternative trading system for stock trading. As an Electronic Communication Networks exclude broker-dealers’ internal crossover networks — that is, systems that match orders in private using public exchange pricing.
Electronic Communication networks s have increased rivalry with institutional trading systems as alternative trading platforms. Alternative trading systems have been discovered to offer lower costs.
![:arrow_right: :arrow_right:]() Trading In Currencies
Trading In Currencies
Matchbook fx, situated in New York, was the first Electronic Communication Network for internet currency trading. All of the prices were established and given by matchbook fx’s traders/users, including banks, using its Electronic Communication Network at the time.
It was highly remarkable at the time since it allowed buy-side fx market players, who had previously just been “price takers,” to become price creators as well.
Summary
Technological advancements have impacted electronic communication between employees in any business. CEOs of multinational firms can connect with one another via the Internet.
Eight Most Secure Communication Methods
Fast and contemporary communication raises the danger of privacy invasion and security problems. Communication is far from private, whether a significant technological business searching for demographic data or a government monitoring speech.
Here’s a rundown of the ten most prevalent modes of communication and how secure they are:
![:one: :one:]() The Internet
The Internet
What you post on social media is visible to my grandma as well. In terms of social media privacy, Facebook has been the elephant in the room. With controversy after the scandal involving privacy, this elephant has shattered many dishes.
Although messaging tools are available on Facebook, Twitter, Instagram, and practically every other social network, their security are uncertain.
Safe option: there are social networking platforms that have pitched themselves as a safe alternative. Nextdoor necessitates address verification. It renders it private in terms of the location of those who view your communications.
![:two: :two:]() Email
Email
Email breaches occur regularly. Recently, 773 million outlook emails were compromised. Because breaches are so widespread, a website allows consumers to check if their email address is one of the almost 8 billion email addresses on file that have been hacked.
Emails are exposed to advertising and data analysis in addition to breaches. Emails for personal use, such as Gmail, include default settings that allow marketers to contact you depending on the content of your email. If requested, emails from a corporation can be read by it and management.
![:three: :three:]() Apps For Chatting
Apps For Chatting
Chat programs provide quick chats for folks who do not want to pick up the phone or move around. These are often used on desktop and mobile devices. When used on a mobile device, the security features of these chat applications are identical to cell phone calls.
Most chat apps use encryption, but they are also subject to sim ■■■■■■■■■ and the person on the other end of the conversation being insecure.
Famous examples include messaging networks such as WhatsApp and signal, which promote security as a motivation to utilize their services.
![:four: :four:]() Telephone Calls
Telephone Calls
If law enforcement obtains a warrant, they may tap your phone. Passive monitoring on your phone may occur, and your call logs and data may be captured. Recording phone calls is lawful in many places as long as one party is informed.
Sim card ■■■■■■■■■ allows data saved on your phone and call records to be hijacked with a little social engineering and spoofing. The numerous ways in which a phone or a call might be intercepted make it susceptible.
![:five: :five:]() Walkie-talkie
Walkie-talkie
This one has the extra benefit of allowing you to employ radio jargon such as “over and out” or “10-4.” Radios are a low-tech way of communicating with others. Anybody with a radio can intercept messages if they are not encrypted.
Even encrypted communications can leak some information. The standard in 2-way radios has been criticized for being insecure. The more ancient components of radio, on the other hand, keep it concealed from modern eyes.
![:six: :six:]() Hand Writing Notes
Hand Writing Notes
Tampering with the mail is against the law. That legal protection shields your correspondence from the majority of curious eyes. Undeliverable or lost mail can, however, occur. In 2010, 4.7 percent of mail was returned as undeliverable.
The total amount of lost mail cannot be calculated. If your email gets through without being intercepted, the message’s privacy is preserved. To keep it safe from beginning to finish, request that the receiver shred the message after reading it.
![:seven: :seven:]() Fax Machine
Fax Machine
Fax machines, like the payphone and two-way radio, are relics of the past. Except in exceptional government cases, these gadgets are not encrypted. The method of intercepting a fax machine, on the other hand, is intimidating because the transmission mechanism is located outside of the internet.
![:eight: :eight:]() Hidden Messages
Hidden Messages
If the recipient of the communication is unknown, a visible message can be secure. Sometimes the most apparent signals are right in front of us. Graffiti left by thousands of individuals can have meaning for the intended recipients.
A visible message can also be disguised in various media, such as a book or a billboard. The meanings embedded in logos are a fun example. These messages are sometimes known as “easter eggs,” referring to the surprise of discovering a concealed message.
Summary
An Electronic Communication Network connects buyers and sellers directly by removing the need for a broker or investment bank. Electronic Communication Network s profit on price discrepancies in stocks and currencies exchanged.
Frequently Asked Questions
People usually ask many questions about Electronic Communication Network (ECN). A few of them are discussed below:
1. What does an Electronic Communication Network look like?
An Electronic Communication Network can offer automated transactions and quotes for securities, including those traded on exchanges. Instinet, selection, island, archipelago, brut, and Bloomberg trade book are examples of Electronic Communication Networks.
2. What is the process of Electronic Communication Network trading?
An Electronic Communication Network is a computerized system that immediately publishes orders placed by market participants to third parties and individual traders.
Those orders are then performed automatically by matching purchase and sell orders at the greatest available price. Electronic Communication Network trading is a highly efficient procedure that employs cutting-edge technology.
3. Is there an Electronic Communication Network cost levied by CIBC?
No, Electronic Communication Network cost does not levied by CIBC. When you consider that questrade charges, Electronic Communication Network costs while CIBC does not, the margin between the two institutions narrows much more.
4. What exactly is an Electronic Communication Network code?
ECN codes are assigned to about 98 percent of all products traded on a global scale. Electronic communication networks are used to identify specific products that are subject to export control restrictions.
They only target a small number of objects, often referred to as dual-use items since they may be employed for commercial and military reasons.
5. What exactly is an Electronic Communication Network trading account?
A real Electronic Communication Network (ECN) trading account is a pure order-matching achievement system.
The account provider charges a premium per transaction rather than artificially inflating the raw spread during the order-matching process.
Conclusion
Communication that occurs outside from the watchful eye of a modern computer is considered off-the-grid and so immune to digital surveillance. If you communicate via a digital device, ensure end-to-end encryption and that the individual receiving the communication is verified.


