DMARC - How To Discuss
DMARC
Domain-based Message Authentication, Reporting and Compliance (DMARC) is a widely recognized email protocol that helps individuals and businesses protect their email addresses and domains from misuse by third parties. This helps to recognize that the email you have sent is yours. This method of email authentication protects both senders and recipients from activities such as phishing, spam, and phishing.
- What is DMARD?
- Why is DMARC important?
- dmarc background
- DMARC history
- How DMARC Email Verification Works
- Your DMARC Input
- Expand DMARC
- DMARC Restrictions
- word list
- DMARC
DMARC
Domain-based Message Authentication, Reporting and Compliance (DMARC) is a widely recognized email protocol that helps individuals and businesses protect their email addresses and domains from misuse by third parties. This helps recognize that the email you sent was sent by you. This method of email authentication protects both senders and recipients from activities such as phishing, spam, and phishing.
What is DMARC?
DMARC uses Sender Policy Framework (SPF) and Domain Key Identified Mail (DKIM) to assess the authenticity of email messages. Together, these tools prevent activities such as phishing and domain spoofing. Phishing is a cyber in which someone impersonates a trusted organization, such as a bank, government agency, or even their own employer, in order to attempt to collect sensitive information such as your credit card information or phone number. Domain spoofing is a form of phishing that uses a fake email address or domain to appear legitimate.
DMARC allows domain owners to control how an email sent from that domain is treated if it does not contain the correct information. For example, unauthenticated e-mail messages can be blocked or sent directly to the spam folder, depending on the settings configured in the records for that e-mail address domain.
Why is DMARC important?
Spammers and phishers have a lot to gain from compromising user accounts. By accessing passwords, credit card details, bank accounts and other financial instruments, attackers can easily access their victims' money without realizing that they have been scammed.
Email is a very attractive and common target, especially for phishing. Even something as simple as including a famous brand logo in an email can lead some recipients to believe they have received a legitimate message.
DMARC is working to solve this problem on a large scale. In fact, free email services like Google, Yahoo, or Hotmail cannot scan every email that goes through their servers to determine which emails are allowed and which may be fraudulent.
SPF and DKIM records can be useful, but these processes are themselves limited. Combined with DMARC, these protocols help senders and recipients work together to better protect email.
DMARC offers 3 key benefits: security, reputation and visibility.
Security
In addition to protecting customers, using DMARC benefits the entire messaging community. By laying the foundation for consistent policies for unauthenticated email processing, DMARC helps make the email ecosystem more reliable and secure.
Call
DMARC protects trademarks by acting as a gatekeeper. This prevents attackers from spoofing your domain and sending emails that appear to be your brand. Posting your DMARC entry can improve your reputation.
Visibility
DMARC gives you more information about your email program and lets you know the identity of anyone sending email from your domain.
DMARC context
To understand DMARC, it is important to understand the basics of SPF and DKIM, as well as Domain Name System (DNS) records. DMARC uses the SPF and DKIM methods.
Frame/sec
SPF helps detect fraud by verifying the return address in emails. This email address is also known as the sender or sender address.
When an email cannot be sent to the recipient after multiple attempts or a delay, a notification of this error is usually sent to the sender's address.
This is how the return path address is used to verify emails.
How FPS works
Domain owners can control which email servers their domain can send messages from by configuring their SPF protocols.
- SPF information is entered in the TXT record to determine which mail servers can send mail for the domain.
- The incoming mail server receives the new mail and checks the rules written for the domain of the reverse path email address. The incoming mail server compares the IP address of the mail sender with the domains and/or IP addresses recorded in the SPF record.
- The receiving server uses the rules specified in the sender's SPF record to determine whether to accept, reject, or report the message.
DKIM
DKIM is an email authentication method that uses an encrypted digital signature to protect email content from unauthorized access. DKIM signatures are added to email messages as headers and are secured with public key cryptography.
When the receiving server determines that an email has a valid DKIM signature, it can verify that the email and its attachments have not been modified. This process is often invisible to end users, such as the intended recipient of an email message.
How DKIM works
How DKIM signatures are verified:
- The domain owner publishes a unique cryptographic key in the form of a TXT record in the domain's DNS record.
- When a message is sent from an outgoing server, it generates a unique DKIM signature and appends it to the header.
- Incoming servers receive an encrypted hash of the message body.
- The receiving server first looks up the DKIM public key specified in the DKIM signature and stored in DNS records.
- The key is used to decrypt the hash, after which a new hash of the message body is generated and compared with the original attached by the sender.
- If the two hashes match, they can confirm that the message was not modified in transit.
Record
The type of DNS record that points domains to an IP address is called an address record. When IPv4 addresses are used, this item is called item A.
CNAME record
You can add a CNAME record to your DNS settings if you want to set a web address, verify domain ownership, reset an administrator password, and more.
History of DMARC
SPF and DKIM were developed several years ago to protect the messaging ecosystem. Although the use of these tools has increased over time, fraudulent and deceptive emails remain a common problem. DMARC was created to solve several common problems:
- Senders with multiple email delivery systems have had great difficulty working with SPF and DKIM.
- When a combination of verified, unauthenticated, and misaligned emails are sent from the same domain, receiving servers must distinguish between legitimate and potentially fraudulent emails. This tends to trigger spam algorithms, causing fraudulent messages to end up in mailboxes.
- With SPF and DKIM, senders get little feedback about their email authentication implementations. If email isn't bounced, senders won't be able to see how many legitimate messages are sent without authentication or how many fraudulent emails are sent from your domain.
- Even if senders have secured their email authentication infrastructure, email recipients are programmed to accept some unauthenticated messages because legitimate, unsigned messages can get through.
To solve these problems, sender and receiver must exchange information with each other. Ideally, recipients provide reporting information to senders, and senders tell recipients what to do when they receive unverified messages.
DMARC is based on the idea that senders and recipients work together to improve senders' email authentication methods and enable recipients to reject unauthenticated messages.
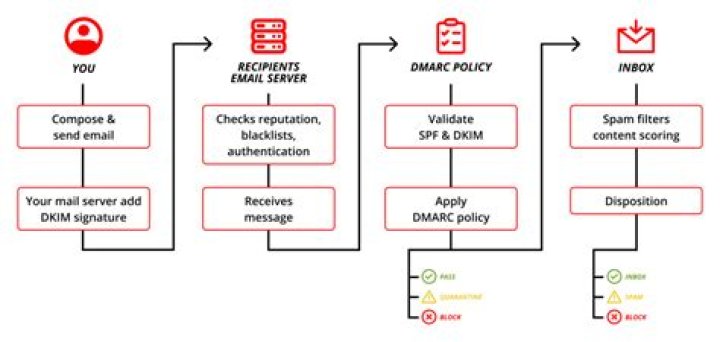
How DMARC Email Verification Works
DMARC can be integrated into existing authentication processes for inbound emails. This helps recipients determine if the message matches what they know about the sender.
If the message is misaligned, the receiving server can check the DMARC record to find out how to handle the misaligned message. Here's an example of this flow for a recipient using SPF and DKIM and its own spam filters (global settings):
- The user writes and sends an email.
- The sending server inserts a DKIM header.
- The sending server sends an email to the recipient.
- Email passes standard checks (IP block lists, speed limits, reputation checks, etc.).
- The receiving server extracts DKIM verified domains based on headers and envelopes through SPF and applies DMARC policies, forwards, quarantines or rejects the email, and sends a report to the sender's server. In other words, we can say that right now the receiving server is looking for the answer "yes" to 3 important questions:
- Has the DKIM signature been verified?
- Does the message come according to the SPF record of the received IP address?
- Post headers with correct domain alignment?
- Email goes through spam filters and other standard processes.
Therefore, DMARC meets a number of high-level requirements:
- Fewer false positives
- Trusted Authentication Reports
- Less identity theft
- work at scale
While not all receiving servers perform a DMARC check before forwarding a message, large ISPs generally do. DMARC adoption is on the rise.
Your DMARC entry
Along with your DNS records, your DMARC record will be published and available to everyone on the Internet. In this section, I'll explain how to verify a domain's DMARC record and what the parts of the record mean.
Check and decrypt the DMARC item
Verifying a domain for a DMARC record can be done from the command line of a terminal window. For instance:
You can also provide a list of other commercial companies that provide DNS record lookup and analysis, including DMARC verifiers.
V=DMARC1 p=Decline
v=DMARC1
The receiving server looks up the identifier v=DMARC1 by parsing the DNS record of the domain sending the message. If the receiving server does not find this tag, it will not perform DMARC authentication.
p=delete, p=none, p=quarantine
P stands for politics. Registered domains can choose from 3 policies to tell the receiving server what to do with emails that fail SPF and DKIM validation, but claim to come from their domain.
- P=none tells the recipient not to take any action on unauthenticated messages and instead email reports to the mailto: address specified in the DMARC record.
- P=quarantine tells the recipient to quarantine unqualified messages (for example, by sending them directly to the spam or spam filter instead of the inbox).
- P=reject tells the recipient to reject unqualified emails. Only verified emails make it to the inbox. Rejected email is simply rejected.
rua=mailto:
This section tells the receiving server where to send aggregated DMARC reports. The reports provide general information about DMARC issues, but are not very detailed.
call=mail to:
Like rua=mailto:, ruf=mailto: tells the receiving server where to send (detailed) DMARC error analysis reports. These reports are sent to the domain administrator in real time and contain detailed information about each incident.
fo=
This section lists one of the many settings associated with the survey report options:
- 0 generates reports when all authentication mechanisms fail to return a successful DMARC result.
- 1 generates reports when a mechanism fails
- D generates reports when DKIM signatures are not verified
- S generates SPF failure reports
sp=
If the optional sp= value is specified in a DMARC entry, it tells the receiving server whether to apply the DMARC policy to subdomains.
healthy=
In addition, the optional value adkim= sets the DKIM alignment to s (strict) or r (relaxed). Strict means that the DKIM part is only allowed if the d= field in the DKIM signature exactly matches the start address. The relax option allows messages to pass through the DKIM portion if the DKIM d= field matches the root domain of the sender's address and is implicit if adkim= is not specified in the input.
ri=
You can also see the ri= value when viewing a DMARC entry. This value sets the interval for the preferred frequency of aggregated reports, as specified in rua=mailto:.
aspf=
Another optional value, aspf=, sets the required strictness for the SPF alignment to s (strict) or r (relaxed). Strict means that the SPF only matches if the email domain From (also known as SPF From, Envelope, or Bounce Address) exactly matches the header From (also known as Friendly From). A loose setting allows SPF alignment when domain email and domain header use the same organizational domain.
percent=
By using this optional value, the domain owner can test the impact of their DMARC on delivery by setting a percentage of the number of emails sent with a particular policy. This can be useful when you first implement DMARC to measure the difference in the delivery success of emails sent from your domain. For example, p=reject pct=50 means that 50% of emails are subject to the most restrictive policy and the remaining 50% to the next most restrictive policy (in this case quarantine).
DMARC Deployment
, a non-profit initiative promoting the use of DMARC, recommends deploying DMARC by following these 5 steps:- Provide SPF and DKIM.
- Make sure your senders match the correct IDs.
- Place a DMARC entry with the None flag to trigger a data report.
- Analyze the data and make the necessary changes.
- Edit the DMARC policy flags to quarantine or disable them as you gain experience. Use pct= to set the percentage of policy flags to test their effect on delivery.
Once DMARC is implemented, you can test it on the National Institute of Standards and Technology Email Authentication Test page. You can also use this resource to test SPF and DKIM, which can be useful for troubleshooting.
DMARC limits
DMARC is a reliable method of reducing email phishing and spoofing, but it does have some limitations. One of the biggest is that phishing attacks cannot be countered with Display Name Impostors (DNI), which account for a large percentage of email scam attempts.
Also, DMARC cannot protect against spoofing of similar domains. DMARC should be used in conjunction with other email fraud protection protocols.
DMARC is also complicated. Companies with a large number of IT specialists have an advantage here. But there are plenty of resources to teach anyone how to use DMARC. This can be time consuming, but domain owners looking to fix vulnerabilities in their email systems will find it worth it.
It is difficult to say how many organizations will end up using DMARC, although the number is constantly growing. Since the vast majority of successful data breaches come from email, it's clear that things get better when DMARC is widely used.


