Public-key Cryptography - How To Discuss
Public-key Cryptography
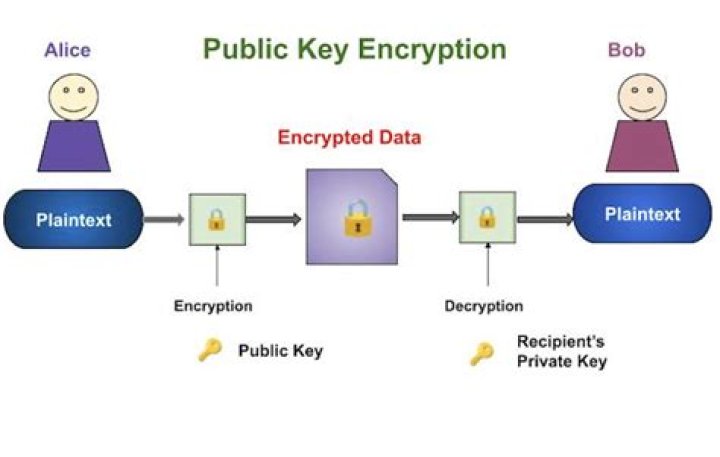
An encryption method designed to overcome the limitations of secret key cryptography (see separate article). Public key cryptography (also known as asymmetric key) uses two mathematically related keys: a public key to encrypt messages and a private key to decrypt them. In a public key system, you communicate privately by encrypting your message with the recipient's public key. Although everyone knows the recipient's public key, there is no point in decrypting an encrypted message with it. Only the associated private key, known only to the recipient, can decrypt the message.
Literal Meanings of Public-key Cryptography
Public:
Meanings of Public:
People in general, regardless of their membership in a particular group.
Inn inn.
It can be seen or identified by anyone in the public domain and can take place without a costume.
It refers to the people as a whole (as opposed to a private group) and refers to the whole country, community, etc.
An official city council, organized or financed by the state on behalf of the municipality.
Open to all members of a particular community, provided by the state or local government and supported by taxpayers' money.
(companies) Listed on a stock exchange.
Available to the program as a whole, not just the class or subclasses.
Sentences of Public
The public should not exceed this point.
Key:
Meanings of Key:
Object to open and close the lock.
An object designed to fit between two other objects (for example, an axle and a wheel) on a machine and maintain its relative orientation.
Critical step or requirement.
A guide that explains symbols or terminology on a map, map, or legend.
A guide to the correct answers on a worksheet or test.
One of many small, usually square keys on a typewriter or computer keyboard that basically correspond to characters in text.
In musical instruments, one of the valve levers is used to select notes, such as a lever punching a in a piece of wood.
On keyboard instruments such as the or piano, one of the levers, or more specifically the open front, is pressed to produce a specific pitch or note.
The lowest note in the scale.
In music theory, the set of melodic and harmonic relationships that exist between the notes of an ideal scale, major or minor.
In music theory and notation, tonality focuses on a specific pitch or several notes together in a specific scale, major or minor.
In music notation, a sign at the top of the staff that indicates the key.
The general tone or tone of a sentence or utterance.
Customize ads to appeal to a specific group or demographic.
Indehiscent monoseed fruit with a wing, like the fruit of the ash and the samara maple.
A hand-held electrical switching device primarily used to transmit Morse code.
A piece of information (such as a passphrase) used to encrypt or decrypt one or more messages.
Password that restricts access to the IRC channel.
In a relational database, a field used as an index in another (not necessarily unique) table.
A value that uniquely identifies an entry in the container.
The free-throw lane, as well as the circle around the free-throw line, where the free-throw lane used to be narrower, giving the area the shape of a skeletal keyhole.
A set of logically organized groups of distinguishing information designed to enable the user to correctly identify a taxon.
Piece of wood used as wedge.
The last floorboard.
Stone castle.
That part of the plaster that sits between the planks and holds the rest in place.
Wooden rail support on a Bullhead rail system.
The degree of roughness or elasticity of a surface after the application of a liquid such as paint or glue.
The thirty-third card of the Lenormand deck.
(Print and Foil) ink layer, especially when compared to the three ink layers cyan, magenta and yellow. See also CMYK.
The color you want to hide or make transparent.
Pick up (the lock) with the key.
Connection (parts of a mechanical assembly) to each other with a wrench to ensure they are mutually aligned.
Marked or shown with an icon indicating it belongs to a class.
(Telegraph and radiotelegraphy) Press (telegraph key).
Operable (radio transmitter switch).
(general entry) enter (information) by typing on the keyboard or numeric keypad.
Vandalism (car, etc.) due to scratches with tools such as a key.
Link (as can be done with key or legend).
Identified as a specific taxon using a key.
Customize (ad) for target audience or demographics.
Vote to vote.
Tie or tie securely or tighten with keys or wedges.
Essential, extremely important.
Important, prominent.
One of a chain of small islands.
Stone or concrete structure in navigable waters used for loading and unloading ships on a quay.
In the International System of Units, the basic unit of mass, intended to represent the mass of a liter of water, but now defined by taking a fixed numerical value for Planck's constant h as 6.62607015 × 1034, expressed in units of kg⋅ m2⋅ s. -1. Symbol: kg.
A unit of weight, such as a mass of one kilogram, is also a weight of one kilogram.
Sentences of Key
The key to solving this problem is persistence.
The key indicates that A stands for accounting.
Some students have cheated with the solution key.
Press the Esc key.
from above along the side of the road.
The door panel should be sanded carefully to ensure good adhesion to the new paint.
Our instructor told us to enter our user details.
He unlocked the car in his parking lot.
He is an important player in his football team.
It draws a number of important conclusions.
The Florida Keys.
Cryptography:
Meanings of Cryptography:
The discipline concerned with the security of communications (e.g., message confidentiality, message integrity, sender authentication, message irrefutability, and many other related topics), regardless of the medium used, such as pen and paper or computer.


